shiro讲义 -Web项目集成Shiro+第五章 Springboot集成Shiro
课程知识点第四章 Web项目集成Shiro1、Web集成原理分析【1】web集成的配置【1.1】新建项目【1.2】pom.xml配置【1.3】web.xml配置【2】SecurityManager对象创建2、Shiro默认过滤器【1】认证相关【2】授权相关3、Web集成完整案例【1】编写pom.xml【2】编写shiro.ini文件【3】编写LoginService【4】编写SecuritySer
文章目录
课程知识点
代码地址https://download.csdn.net/download/guan1843036360/86746065
第四章 Web项目集成Shiro
1、Web集成原理分析
【1】web集成的配置
还记得吗,以前我们在没有与WEB环境进行集成的时候,为了生成SecurityManager对象,是通过手动读取配置文件生成工厂对象,再通过工厂对象获取到SecurityManager的。就像下面代码展示的那样
/**
* @Description 登录方法
*/
private Subject shiroLogin(String loginName,String password) {
//导入权限ini文件构建权限工厂
Factory<SecurityManager> factory = new IniSecurityManagerFactory("classpath:shiro.ini");
//工厂构建安全管理器
SecurityManager securityManager = factory.getInstance();
//使用SecurityUtils工具生效安全管理器
SecurityUtils.setSecurityManager(securityManager);
//使用SecurityUtils工具获得主体
Subject subject = SecurityUtils.getSubject();
//构建账号token
UsernamePasswordToken usernamePasswordToken = new UsernamePasswordToken(loginName, password);
//登录操作
subject.login(usernamePasswordToken);
return subject;
}
不过,现在我们既然说要与WEB集成,那么首先要做的事情就是把我们的shiro.ini这个配置文件交付到WEB环境中,定义shiro.ini文件如下
#声明自定义的realm,且为安全管理器指定realms
[main]
definitionRealm=com.itheima.shiro.realm.DefinitionRealm
securityManager.realms=$definitionRealm
【1.1】新建项目
新建web项目shiro-day01-07web,其中realm、service、resources内容从shiro-day01-06authentication-realm中拷贝即可

【1.2】pom.xml配置
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<groupId>com.itheima.shiro</groupId>
<artifactId>shiro-day01-07web</artifactId>
<version>1.0-SNAPSHOT</version>
<packaging>war</packaging>
<name>shiro-day01-07web Maven Webapp</name>
<!-- FIXME change it to the project's website -->
<url>http://www.example.com</url>
<dependencies>
<dependency>
<groupId>commons-logging</groupId>
<artifactId>commons-logging</artifactId>
<version>1.1.3</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-core</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-web</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>junit</groupId>
<artifactId>junit</artifactId>
<version>4.11</version>
</dependency>
</dependencies>
<build>
<plugins>
<!-- tomcat7插件,命令: mvn tomcat7:run -DskipTests -->
<plugin>
<groupId>org.apache.tomcat.maven</groupId>
<artifactId>tomcat7-maven-plugin</artifactId>
<version>2.2</version>
<configuration>
<uriEncoding>utf-8</uriEncoding>
<port>8080</port>
<path>/platform</path>
</configuration>
</plugin>
<!-- compiler插件, 设定JDK版本 -->
<plugin>
<groupId>org.apache.maven.plugins</groupId>
<artifactId>maven-compiler-plugin</artifactId>
<version>3.1</version>
<configuration>
<source>8</source>
<target>8</target>
<showWarnings>true</showWarnings>
</configuration>
</plugin>
</plugins>
</build>
</project>
【1.3】web.xml配置
<web-app xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns="http://java.sun.com/xml/ns/javaee"
xsi:schemaLocation="http://java.sun.com/xml/ns/javaee http://java.sun.com/xml/ns/javaee/web-app_3_0.xsd"
version="3.0">
<display-name>shiro-day01-07web</display-name>
<!-- 初始化SecurityManager对象所需要的环境-->
<context-param>
<param-name>shiroEnvironmentClass</param-name>
<param-value>org.apache.shiro.web.env.IniWebEnvironment</param-value>
</context-param>
<!-- 指定Shiro的配置文件的位置 -->
<context-param>
<param-name>shiroConfigLocations</param-name>
<param-value>classpath:shiro.ini</param-value>
</context-param>
<!-- 监听服务器启动时,创建shiro的web环境。
即加载shiroEnvironmentClass变量指定的IniWebEnvironment类-->
<listener>
<listener-class>org.apache.shiro.web.env.EnvironmentLoaderListener</listener-class>
</listener>
<!-- shiro的l过滤入口,过滤一切请求 -->
<filter>
<filter-name>shiroFilter</filter-name>
<filter-class>org.apache.shiro.web.servlet.ShiroFilter</filter-class>
</filter>
<filter-mapping>
<filter-name>shiroFilter</filter-name>
<!-- 过滤所有请求 -->
<url-pattern>/*</url-pattern>
</filter-mapping>
</web-app>
【2】SecurityManager对象创建
上面我们集成shiro到web项目了,下面我们来追踪下源码,看下SecurityManager对象是如何创建的
(1)我启动了服务器,监听器捕获到了服务器启动事件。我现在所处的位置EnvironmentLoaderListener监听器的入口处
(2)进入方法内查看,它先根据我们的shiroEnvironmentClass变量的值org.apache.shiro.web.env.IniWebEnvironment,初始化一个shiro环境对象
(3)最后在创建一个SecurityManager对象,再将其绑定到刚才通过字节码创建的Shiro环境对象中



到这来SecurityManager就完成了初始化
2、Shiro默认过滤器
Shiro内置了很多默认的过滤器,比如身份验证、授权等相关的。默认过滤器可以参考org.apache.shiro.web.filter.mgt.DefaultFilter中的枚举过滤器

【1】认证相关
| 过滤器 | 过滤器类 | 说明 | 默认 |
|---|---|---|---|
| authc | FormAuthenticationFilter | 基于表单的过滤器;如“/**=authc”,如果没有登录会跳到相应的登录页面登录 | 无 |
| logout | LogoutFilter | 退出过滤器,主要属性:redirectUrl:退出成功后重定向的地址,如“/logout=logout” | / |
| anon | AnonymousFilter | 匿名过滤器,即不需要登录即可访问;一般用于静态资源过滤;示例“/static/**=anon” | 无 |
【2】授权相关
| 过滤器 | 过滤器类 | 说明 | 默认 |
|---|---|---|---|
| roles | RolesAuthorizationFilter | 角色授权拦截器,验证用户是否拥有所有角色;主要属性: loginUrl:登录页面地址(/login.jsp);unauthorizedUrl:未授权后重定向的地址;示例“/admin/**=roles[admin]” | 无 |
| perms | PermissionsAuthorizationFilter | 权限授权拦截器,验证用户是否拥有所有权限;属性和roles一样;示例“/user/**=perms[“user:create”]” | 无 |
| port | PortFilter | 端口拦截器,主要属性:port(80):可以通过的端口;示例“/test= port[80]”,如果用户访问该页面是非80,将自动将请求端口改为80并重定向到该80端口,其他路径/参数等都一样 | 无 |
| rest | HttpMethodPermissionFilter | rest风格拦截器,自动根据请求方法构建权限字符串(GET=read, POST=create,PUT=update,DELETE=delete,HEAD=read,TRACE=read,OPTIONS=read, MKCOL=create)构建权限字符串;示例“/users=rest[user]”,会自动拼出“user:read,user:create,user:update,user:delete”权限字符串进行权限匹配(所有都得匹配,isPermittedAll) | 无 |
| ssl | SslFilter | SSL拦截器,只有请求协议是https才能通过;否则自动跳转会https端口(443);其他和port拦截器一样; | 无 |
3、Web集成完整案例
基于shiro-day01-07web继续集成
【1】编写pom.xml
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<groupId>com.itheima.shiro</groupId>
<artifactId>shiro-day01-07web</artifactId>
<version>1.0-SNAPSHOT</version>
<packaging>war</packaging>
<name>shiro-day01-07web Maven Webapp</name>
<!-- FIXME change it to the project's website -->
<url>http://www.example.com</url>
<dependencies>
<dependency>
<groupId>commons-logging</groupId>
<artifactId>commons-logging</artifactId>
<version>1.1.3</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-core</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-web</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>junit</groupId>
<artifactId>junit</artifactId>
<version>4.11</version>
</dependency>
<dependency>
<groupId>javax.servlet</groupId>
<artifactId>javax.servlet-api</artifactId>
<version>3.0.1</version>
<scope>provided</scope>
</dependency>
<dependency>
<groupId>jstl</groupId>
<artifactId>jstl</artifactId>
<version>1.2</version>
</dependency>
<dependency>
<groupId>taglibs</groupId>
<artifactId>standard</artifactId>
<version>1.1.2</version>
</dependency>
</dependencies>
<build>
<plugins>
<!-- tomcat7插件,命令: mvn tomcat7:run -DskipTests -->
<plugin>
<groupId>org.apache.tomcat.maven</groupId>
<artifactId>tomcat7-maven-plugin</artifactId>
<version>2.2</version>
<configuration>
<uriEncoding>utf-8</uriEncoding>
<port>8080</port>
<path>/platform</path>
</configuration>
</plugin>
<!-- compiler插件, 设定JDK版本 -->
<plugin>
<groupId>org.apache.maven.plugins</groupId>
<artifactId>maven-compiler-plugin</artifactId>
<version>3.1</version>
<configuration>
<source>8</source>
<target>8</target>
<showWarnings>true</showWarnings>
</configuration>
</plugin>
</plugins>
</build>
</project>
【2】编写shiro.ini文件
#声明自定义的realm,且为安全管理器指定realms
[main]
definitionRealm=com.itheima.shiro.realm.DefinitionRealm
securityManager.realms=$definitionRealm
#用户退出后跳转指定JSP页面
logout.redirectUrl=/login.jsp
#若没有登录,则被authc过滤器重定向到login.jsp页面
authc.loginUrl = /login.jsp
[urls]
/login=anon
#发送/home请求需要先登录
/home= authc
#发送/order/list请求需要先登录
/order-list = roles[admin]
#提交代码需要order:add权限
/order-add = perms["order:add"]
#更新代码需要order:del权限
/order-del = perms["order:del"]
#发送退出请求则用退出过滤器
/logout = logout
【3】编写LoginService
package com.itheima.shiro.service;
import org.apache.shiro.authc.UsernamePasswordToken;
import java.lang.management.LockInfo;
/**
* @Description:登录服务
*/
public interface LoginService {
/**
* @Description 登录方法
* @param token 登录对象
* @return
*/
boolean login(UsernamePasswordToken token);
/**
* @Description 登出方法
*/
void logout();
}
package com.itheima.shiro.service.impl;
import com.itheima.shiro.service.LoginService;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.subject.Subject;
/**
* @Description:登录服务
*/
public class LoginServiceImpl implements LoginService {
@Override
public boolean login(UsernamePasswordToken token) {
Subject subject = SecurityUtils.getSubject();
try {
subject.login(token);
}catch (Exception e){
return false;
}
return subject.isAuthenticated();
}
@Override
public void logout() {
Subject subject = SecurityUtils.getSubject();
subject.logout();
}
}
【4】编写SecurityServiceImpl
package com.itheima.shiro.service.impl;
import com.itheima.shiro.service.SecurityService;
import java.util.ArrayList;
import java.util.HashMap;
import java.util.List;
import java.util.Map;
/**
* @Description:权限服务层
*/
public class SecurityServiceImpl implements SecurityService {
@Override
public Map<String,String> findPasswordByLoginName(String loginName) {
return DigestsUtil.entryptPassword("123");
return map;
}
@Override
public List<String> findRoleByloginName(String loginName) {
List<String> list = new ArrayList<>();
if ("admin".equals(loginName)){
list.add("admin");
}
list.add("dev");
return list;
}
@Override
public List<String> findPermissionByloginName(String loginName) {
List<String> list = new ArrayList<>();
if ("jay".equals(loginName)){
list.add("order:list");
list.add("order:add");
list.add("order:del");
}
return list;
}
}
【5】添加web层内容
【5.1】LoginServlet
package com.itheima.shiro.web;
import com.itheima.shiro.service.LoginService;
import com.itheima.shiro.service.impl.LoginServiceImpl;
import org.apache.shiro.authc.UsernamePasswordToken;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:登录方法
*/
@WebServlet(urlPatterns = "/login")
public class LoginServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
//获取输入的帐号密码
String username = req.getParameter("loginName");
String password = req.getParameter("password");
//封装用户数据,成为Shiro能认识的token标识
UsernamePasswordToken token = new UsernamePasswordToken(username, password);
LoginService loginService = new LoginServiceImpl();
//将封装用户信息的token进行验证
boolean isLoginSuccess = loginService.login(token);
if (!isLoginSuccess) {
//重定向到未登录成功页面
resp.sendRedirect("login.jsp");
return;
}
req.getRequestDispatcher("/home").forward(req, resp);
}
}
【5.2】HomeServlet
package com.itheima.shiro.web;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:系统home页面
*/
@WebServlet(urlPatterns = "/home")
public class HomeServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
req.getRequestDispatcher("home.jsp").forward(req, resp);
}
}
【5.3】OrderAddServlet
package com.itheima.shiro.web;
import com.itheima.shiro.service.LoginService;
import com.itheima.shiro.service.impl.LoginServiceImpl;
import org.apache.shiro.authc.UsernamePasswordToken;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:添加页码
*/
@WebServlet(urlPatterns = "/order-add")
public class OrderAddServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
req.getRequestDispatcher("order-add.jsp").forward(req, resp);
}
}
【5.4】OrderListServlet
package com.itheima.shiro.web;
import com.itheima.shiro.service.LoginService;
import com.itheima.shiro.service.impl.LoginServiceImpl;
import org.apache.shiro.authc.UsernamePasswordToken;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:订单列表
*/
@WebServlet(urlPatterns = "/order-list")
public class OrderListServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
req.getRequestDispatcher("order-list.jsp").forward(req, resp);
}
}
【5.5】LogoutServlet
package com.itheima.shiro.web;
import com.itheima.shiro.service.LoginService;
import com.itheima.shiro.service.impl.LoginServiceImpl;
import org.apache.shiro.authc.UsernamePasswordToken;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:登出
*/
@WebServlet(urlPatterns = "/logout")
public class LogoutServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
LoginService loginService = new LoginServiceImpl();
loginService.logout();
}
}
【6】添加JSP
login.jsp登录页面
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>Title</title>
</head>
<body>
<form method="post" action="${pageContext.request.contextPath}/login">
<table>
<tr>
<th>登陆名称</th>
<td><input type="text" name="loginName"></td>
</tr>
<tr>
<th>密码</th>
<td><input type="password" name="password"></td>
</tr>
<tr>
<td colspan="2">
<input type="submit" value="提交"/>
</td>
</tr>
</table>
</form>
</body>
</html>
home.jsp系统页
<%@ taglib prefix="c" uri="http://java.sun.com/jsp/jstl/core" %>
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<title></title>
</head>
<body>
<h6>
<a href="${pageContext.request.contextPath}/logout">退出</a>
<a href="${pageContext.request.contextPath}/order-list">列表</a>
<a href="${pageContext.request.contextPath}/order-add">添加</a>
</h6>
</body>
</html>
order-add.jsp订单添加(伪代码)
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>Title</title>
</head>
<body>
添加页面
</body>
</html>
order-list.jsp订单列表
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<%--导入jstl标签库--%>
<%@ taglib prefix="c" uri="http://java.sun.com/jsp/jstl/core" %>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>用户列表jsp页面</title>
<style>
table {border:1px solid #000000}
table th{border:1px solid #000000}
table td{border:1px solid #000000}
</style>
</head>
<body>
<table cellpadding="0" cellspacing="0" width="80%">
<tr>
<th>编号</th>
<th>公司名称</th>
<th>信息来源</th>
<th>所属行业</th>
<th>级别</th>
<th>联系地址</th>
<th>联系电话</th>
</tr>
<tr>
<td>1</td>
<td>传智播客</td>
<td>网络营销</td>
<td>互联网</td>
<td>普通客户</td>
<td>津安创意园</td>
<td>0208888887</td>
</tr>
<tr>
<td>2</td>
<td>黑马程序员</td>
<td>j2ee</td>
<td>互联网</td>
<td>VIP客户</td>
<td>津安创意园</td>
<td>0208888887</td>
</tr>
<tr>
<td>3</td>
<td>黑马程序员</td>
<td>大数据</td>
<td>互联网</td>
<td>VIP客户</td>
<td>津安创意园</td>
<td>0208888887</td>
</tr>
</table>
</body>
</html>
【7】测试
【7.1】启动


点击apply然后点击OK

【7.2】登录过滤
访问http://localhost:8080/platform/home的时候,会被

【7.3】角色过滤
使用“admin”用户登录,密码:123

根据SecurityServiceImpl我们可以知道使用admin账号

登录成功之后:
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-kzzdfOz1-1665144667169)(image\1580713214523.png)]](https://i-blog.csdnimg.cn/blog_migrate/a8b37b39785514e1f217a4af4d3d36b7.png)
此时点击“列表”,因为当前admin用户是有admin角色

所有可以正常访问

点击“添加”,因为当前admin用户是没有order:add的资源
所以回401
【7.4】资源过滤
点击“退出”

使用“jay”用户登录,密码为123

点击“添加”
因为SecurityServiceImpl中为jay用户添加如下的资源

点击“添加”之后正常访问

点击“列表”之后,因为“jay”用户满意“admin”角色,所以访问受限

4、web项目授权
前面我们学习了基于ini文件配置方式来完成授权,下面我们来看下其他2种方式的授权
【1】基于代码
【1.1】登录相关
| Subject 登录相关方法 | 描述 |
|---|---|
| isAuthenticated() | 返回true 表示已经登录,否则返回false。 |
【1.2】角色相关
| Subject 角色相关方法 | 描述 |
|---|---|
| hasRole(String roleName) | 返回true 如果Subject 被分配了指定的角色,否则返回false。 |
| hasRoles(List roleNames) | 返回true 如果Subject 被分配了所有指定的角色,否则返回false。 |
| hasAllRoles(CollectionroleNames) | 返回一个与方法参数中目录一致的hasRole 结果的集合。有性能的提高如果许多角色需要执行检查(例如,当自定义一个复杂的视图)。 |
| checkRole(String roleName) | 安静地返回,如果Subject 被分配了指定的角色,不然的话就抛出AuthorizationException。 |
| checkRoles(CollectionroleNames) | 安静地返回,如果Subject 被分配了所有的指定的角色,不然的话就抛出AuthorizationException。 |
| checkRoles(String… roleNames) | 与上面的checkRoles 方法的效果相同,但允许Java5 的var-args 类型的参数 |
【1.3】资源相关
| Subject 资源相关方法 | 描述 |
|---|---|
| isPermitted(Permission p) | 返回true 如果该Subject 被允许执行某动作或访问被权限实例指定的资源,否则返回false |
| isPermitted(List perms) | 返回一个与方法参数中目录一致的isPermitted 结果的集合。 |
| isPermittedAll(Collectionperms) | 返回true 如果该Subject 被允许所有指定的权限,否则返回false有性能的提高如果需要执行许多检查(例如,当自定义一个复杂的视图) |
| isPermitted(String perm) | 返回true 如果该Subject 被允许执行某动作或访问被字符串权限指定的资源,否则返回false。 |
| isPermitted(String…perms) | 返回一个与方法参数中目录一致的isPermitted 结果的数组。有性能的提高如果许多字符串权限检查需要被执行(例如,当自定义一个复杂的视图)。 |
| isPermittedAll(String…perms) | 返回true 如果该Subject 被允许所有指定的字符串权限,否则返回false。 |
| checkPermission(Permission p) | 安静地返回,如果Subject 被允许执行某动作或访问被特定的权限实例指定的资源,不然的话就抛出AuthorizationException 异常。 |
| checkPermission(String perm) | 安静地返回,如果Subject 被允许执行某动作或访问被特定的字符串权限指定的资源,不然的话就抛出AuthorizationException 异常。 |
| checkPermissions(Collection perms) | 安静地返回,如果Subject 被允许所有的权限,不然的话就抛出AuthorizationException 异常。有性能的提高如果需要执行许多检查(例如,当自定义一个复杂的视图) |
| checkPermissions(String… perms) | 和上面的checkPermissions 方法效果相同,但是使用的是基于字符串的权限。 |
【1.4】案例
【1.4.1】创建项目
拷贝shiro-day01-07web新建shiro-day01-08web-java

【1.4.2】修改shiro.ini
#声明自定义的realm,且为安全管理器指定realms
[main]
definitionRealm=com.itheima.shiro.realm.DefinitionRealm
securityManager.realms=$definitionRealm
#用户退出后跳转指定JSP页面
logout.redirectUrl=/login.jsp
#若没有登录,则被authc过滤器重定向到login.jsp页面
authc.loginUrl = /login.jsp
[urls]
/login=anon
#发送/home请求需要先登录
#/home= authc
#发送/order/list请求需要先登录
#/order-list = roles[admin]
#提交代码需要order:add权限
#/order-add = perms["order:add"]
#更新代码需要order:del权限
#/order-del = perms["order:del"]
#发送退出请求则用退出过滤器
/logout = logout
【1.4.3】登录相关
修改HomeServlet的doPost方法
package com.itheima.shiro.web;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.subject.Subject;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:系统home页面
*/
@WebServlet(urlPatterns = "/home")
public class HomeServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
//通过subjectd对象去判断是否登录
Subject subject = SecurityUtils.getSubject();
boolean flag = subject.isAuthenticated();
if (flag){
resp.sendRedirect("home.jsp");
}else {
req.getRequestDispatcher("/login").forward(req, resp);
}
}
}
访问http://localhost:8080/platform/home 进行debug

此时我们通过subject.isAuthenticated()判断是否登录,如果登录则重定向到home.jsp,如果没有登录则转发到/login对应的servlet
【1.4.4】角色相关
修改OrderListServlet的doPost方法,判断是否有admin角色,如果有则转发order-list.jsp,没有则转发/login
package com.itheima.shiro.web;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.subject.Subject;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:订单列表
*/
@WebServlet(urlPatterns = "/order-list")
public class OrderListServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
Subject subject = SecurityUtils.getSubject();
//判断当前角色
boolean flag = subject.hasRole("admin");
if (flag){
req.getRequestDispatcher("order-list.jsp").forward(req, resp);
}else {
req.getRequestDispatcher("/login").forward(req, resp);
}
}
}
访问http://localhost:8080/platform/order-list

因为此时我未登录,也就是说当前没有admin角色,这是通过subject.hasRole(“admin”)返回未false
【1.4.5】资源相关
修改OrderAddServlet
package com.itheima.shiro.web;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.subject.Subject;
import javax.servlet.ServletException;
import javax.servlet.annotation.WebServlet;
import javax.servlet.http.HttpServlet;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
/**
* @Description:添加页码
*/
@WebServlet(urlPatterns = "/order-add")
public class OrderAddServlet extends HttpServlet {
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
doPost(req, resp);
}
@Override
protected void doPost(HttpServletRequest req, HttpServletResponse resp)
throws ServletException, IOException {
Subject subject = SecurityUtils.getSubject();
//判断是否有对应资源
boolean flag = subject.isPermitted("order:add");
if (flag){
req.getRequestDispatcher("order-add.jsp").forward(req, resp);
}else {
req.getRequestDispatcher("/login").forward(req, resp);
}
}
}
访问http://localhost:8080/platform/order-add

因为此时我未登录,也就是说当前没有order:add资源,通过 subject.isPermitted(“order:add”)返回未false
【2】基于Jsp标签
【2.1】使用方式
Shiro提供了一套JSP标签库来实现页面级的授权控制, 在使用Shiro标签库前,首先需要在JSP引入shiro标签:
<%@ taglib prefix="shiro" uri="http://shiro.apache.org/tags" %>
【2.2】相关标签
| 标签 | 说明 |
|---|---|
| < shiro:guest > | 验证当前用户是否为“访客”,即未认证(包含未记住)的用户 |
| < shiro:user > | 认证通过或已记住的用户 |
| < shiro:authenticated > | 已认证通过的用户。不包含已记住的用户,这是与user标签的区别所在 |
| < shiro:notAuthenticated > | 未认证通过用户。与guest标签的区别是,该标签包含已记住用户 |
| < shiro:principal /> | 输出当前用户信息,通常为登录帐号信息 |
| < shiro:hasRole name=“角色”> | 验证当前用户是否属于该角色 |
| < shiro:lacksRole name=“角色”> | 与hasRole标签逻辑相反,当用户不属于该角色时验证通过 |
| < shiro:hasAnyRoles name=“a,b”> | 验证当前用户是否属于以下任意一个角色 |
| <shiro:hasPermission name=“资源”> | 验证当前用户是否拥有制定权限 |
| <shiro:lacksPermission name=“资源”> | 与permission标签逻辑相反,当前用户没有制定权限时,验证通过 |
【2.3】案例
【2.3.1】新建项目
拷贝shiro-day01-08web-java新建shiro-day01-09web-jsp-taglib项目

【2.3.2】修改home.jsp
<%@ taglib prefix="c" uri="http://java.sun.com/jsp/jstl/core" %>
<%@ taglib prefix="shiro" uri="http://shiro.apache.org/tags" %>
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<title></title>
</head>
<body>
<h6>
<a href="${pageContext.request.contextPath}/logout">退出</a>
<shiro:hasRole name="admin">
<a href="${pageContext.request.contextPath}/order-list">列表</a>
</shiro:hasRole>
<shiro:hasPermission name="order:add">
<a href="${pageContext.request.contextPath}/order-add">添加</a>
</shiro:hasPermission>
</h6>
</body>
</html>
【2.3.3】测试
访问http://localhost:8080/platform/login
使用admin/123登录

这个时候我们只能看见“列表”,看不见“添加”,点击“退出”
使用jay/123登录

这个时候我们只能看见“添加”,看不见“列表”,点击“退出”
需要注意的是,这里只是页面是否显示内容,不能防止盗链的发生
第五章 Springboot集成Shiro
1、技术栈
主框架:springboot
响应层:springMVC
持久层:mybatis
事务控制:jta
前端技术:easyui
2、数据库设计
【1】数据库图解

sh_user:用户表,一个用户可以有多个角色
sh_role:角色表,一个角色可以有多个资源
sh_resource:资源表
sh_user_role:用户角色中间表
sh_role_resource:角色资源中间表
【2】数据库脚本
sh_user
CREATE TABLE `sh_user` (
`ID` varchar(36) NOT NULL COMMENT '主键',
`LOGIN_NAME` varchar(36) DEFAULT NULL COMMENT '登录名称',
`REAL_NAME` varchar(36) DEFAULT NULL COMMENT '真实姓名',
`NICK_NAME` varchar(36) DEFAULT NULL COMMENT '昵称',
`PASS_WORD` varchar(150) DEFAULT NULL COMMENT '密码',
`SALT` varchar(36) DEFAULT NULL COMMENT '加密因子',
`SEX` int(11) DEFAULT NULL COMMENT '性别',
`ZIPCODE` varchar(36) DEFAULT NULL COMMENT '邮箱',
`ADDRESS` varchar(36) DEFAULT NULL COMMENT '地址',
`TEL` varchar(36) DEFAULT NULL COMMENT '固定电话',
`MOBIL` varchar(36) DEFAULT NULL COMMENT '电话',
`EMAIL` varchar(36) DEFAULT NULL COMMENT '邮箱',
`DUTIES` varchar(36) DEFAULT NULL COMMENT '职务',
`SORT_NO` int(11) DEFAULT NULL COMMENT '排序',
`ENABLE_FLAG` varchar(18) DEFAULT NULL COMMENT '是否有效',
PRIMARY KEY (`ID`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='用户表';
sh_role
CREATE TABLE `sh_role` (
`ID` varchar(36) NOT NULL COMMENT '主键',
`ROLE_NAME` varchar(36) DEFAULT NULL COMMENT '角色名称',
`LABEL` varchar(36) DEFAULT NULL COMMENT '角色标识',
`DESCRIPTION` varchar(200) DEFAULT NULL COMMENT '角色描述',
`SORT_NO` int(36) DEFAULT NULL COMMENT '排序',
`ENABLE_FLAG` varchar(18) DEFAULT NULL COMMENT '是否有效',
PRIMARY KEY (`ID`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='用户角色表';
sh_resource
CREATE TABLE `sh_resource` (
`ID` varchar(36) NOT NULL COMMENT '主键',
`PARENT_ID` varchar(36) DEFAULT NULL COMMENT '父资源',
`RESOURCE_NAME` varchar(36) DEFAULT NULL COMMENT '资源名称',
`REQUEST_PATH` varchar(200) DEFAULT NULL COMMENT '资源路径',
`LABEL` varchar(200) DEFAULT NULL COMMENT '资源标签',
`ICON` varchar(20) DEFAULT NULL COMMENT '图标',
`IS_LEAF` varchar(18) DEFAULT NULL COMMENT '是否叶子节点',
`RESOURCE_TYPE` varchar(36) DEFAULT NULL COMMENT '资源类型',
`SORT_NO` int(11) DEFAULT NULL COMMENT '排序',
`DESCRIPTION` varchar(200) DEFAULT NULL COMMENT '描述',
`SYSTEM_CODE` varchar(36) DEFAULT NULL COMMENT '系统code',
`IS_SYSTEM_ROOT` varchar(18) DEFAULT NULL COMMENT '是否根节点',
`ENABLE_FLAG` varchar(18) DEFAULT NULL COMMENT '是否有效',
PRIMARY KEY (`ID`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='资源表';
sh_role_resource
CREATE TABLE `sh_role_resource` (
`ID` varchar(36) NOT NULL,
`ENABLE_FLAG` varchar(18) DEFAULT NULL,
`ROLE_ID` varchar(36) DEFAULT NULL,
`RESOURCE_ID` varchar(36) DEFAULT NULL,
PRIMARY KEY (`ID`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='角色资源表';
sh_user_role
CREATE TABLE `sh_user_role` (
`ID` varchar(36) NOT NULL,
`ENABLE_FLAG` varchar(18) DEFAULT NULL,
`USER_ID` varchar(36) DEFAULT NULL,
`ROLE_ID` varchar(36) DEFAULT NULL,
PRIMARY KEY (`ID`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='用户角色表';
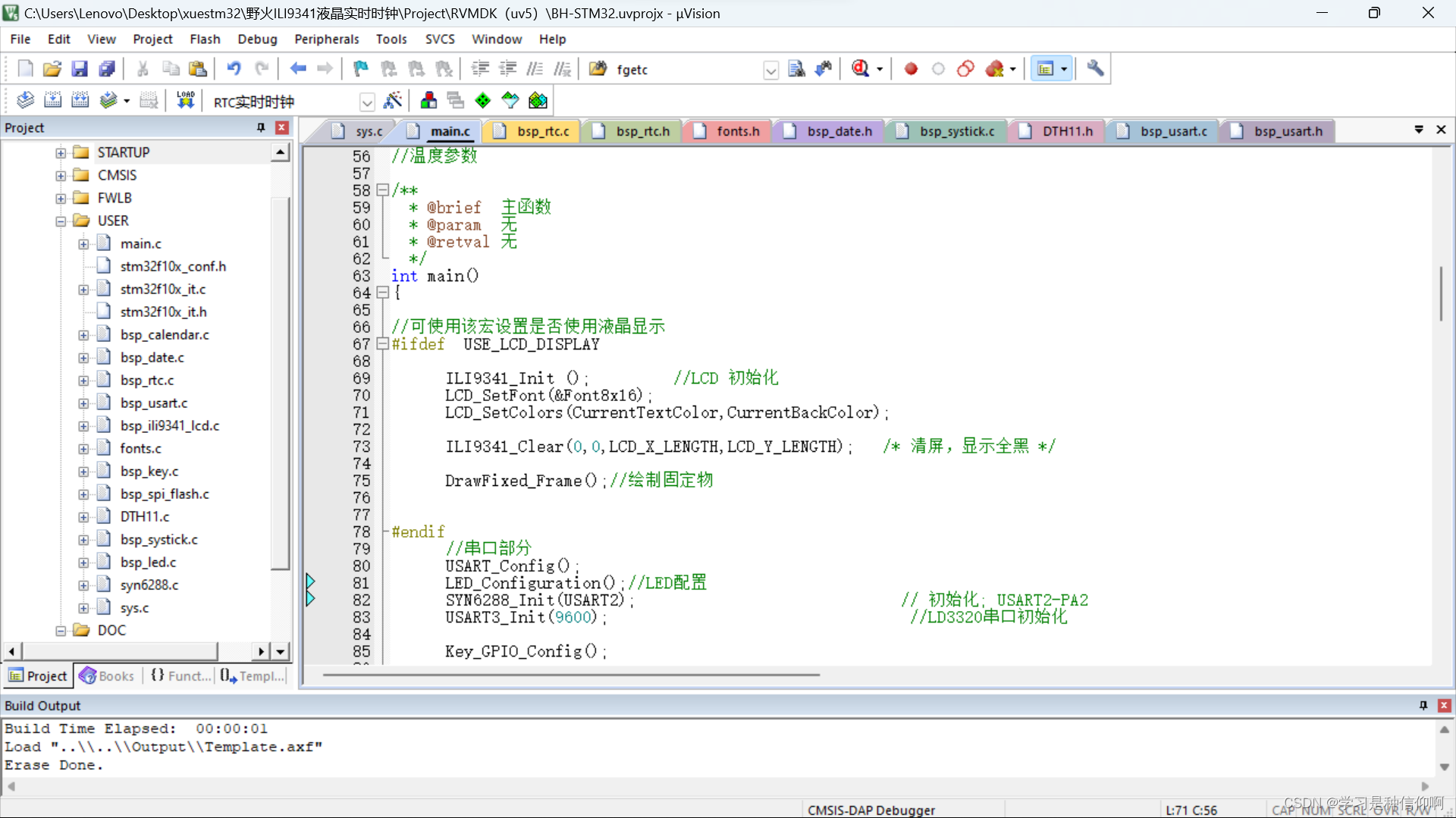
3、项目骨架
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-yzZ7SlUg-1665144667175)(image\1581062691221.png)]](https://i-blog.csdnimg.cn/blog_migrate/53cdd9c0188a3035ebdaf8409063c481.png)
4、ShiroDbRealm定义
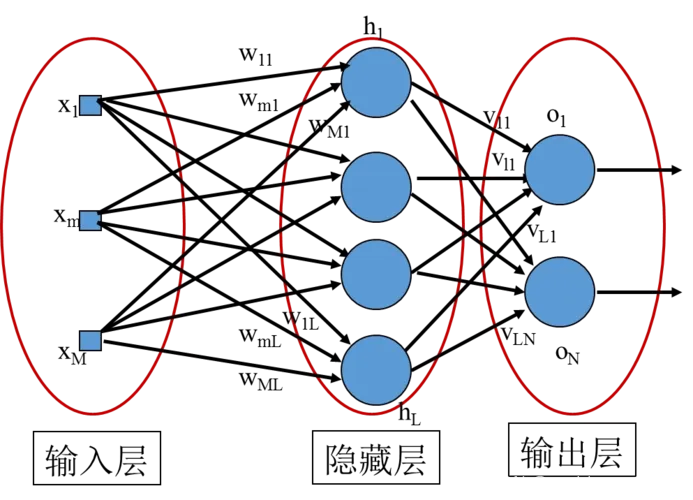
【1】图解
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-MFcjQlOI-1665144667176)(image\1583895738811.png)]](https://i-blog.csdnimg.cn/blog_migrate/8b44ffe8663564729cbd2a8a73c304e3.png)
【2】原理分析
(1)、ShiroDbRealmImpl继承ShiroDbRealm向上继承AuthorizingRealm,ShiroDbRealmImpl实例化时会创建密码匹配器HashedCredentialsMatcher实例,HashedCredentialsMatcher指定hash次数与方式,交于AuthenticatingRealm
(2)、调用login方法后,最终调用doGetAuthenticationInfo(AuthenticationToken authcToken)方法,拿到SimpleToken的对象,调用UserBridgeService的查找用户方法,把ShiroUser对象、密码和salt交于SimpleAuthenticationInfo去认证
(3)、访问需要鉴权时,调用doGetAuthorizationInfo(PrincipalCollection principals)方法,然后调用UserBridgeService的授权验证
【3】核心类代码
【3.1】ShiroDbRealm
package com.itheima.shiro.core;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import javax.annotation.PostConstruct;
/**
*
* @Description shiro自定义realm
*/
public abstract class ShiroDbRealm extends AuthorizingRealm {
/**
* @Description 认证
* @param authcToken token对象
* @return
*/
public abstract AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authcToken) ;
/**
* @Description 鉴权
* @param principals 令牌
* @return
*/
public abstract AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principals);
/**
* @Description 密码匹配器
*/
@PostConstruct
public abstract void initCredentialsMatcher() ;
}
【3.2】ShiroDbRealmImpl
package com.itheima.shiro.core.impl;
import com.itheima.shiro.constant.SuperConstant;
import com.itheima.shiro.core.base.ShiroUser;
import com.itheima.shiro.core.base.SimpleToken;
import com.itheima.shiro.core.ShiroDbRealm;
import com.itheima.shiro.core.bridge.UserBridgeService;
import com.itheima.shiro.pojo.User;
import com.itheima.shiro.utils.BeanConv;
import com.itheima.shiro.utils.DigestsUtil;
import com.itheima.shiro.utils.EmptyUtil;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.SimpleAuthenticationInfo;
import org.apache.shiro.authc.UnknownAccountException;
import org.apache.shiro.authc.credential.HashedCredentialsMatcher;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.util.ByteSource;
import org.springframework.beans.factory.annotation.Autowired;
/**
* @Description:自定义shiro的实现
*/
public class ShiroDbRealmImpl extends ShiroDbRealm {
@Autowired
private UserBridgeService userBridgeService;
/**
* @Description 认证方法
* @param authcToken 校验传入令牌
* @return AuthenticationInfo
*/
@Override
public AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authcToken) {
SimpleToken token = (SimpleToken)authcToken;
User user = userBridgeService.findUserByLoginName(token.getUsername());
if(EmptyUtil.isNullOrEmpty(user)){
throw new UnknownAccountException("账号不存在");
}
ShiroUser shiroUser = BeanConv.toBean(user, ShiroUser.class);
shiroUser.setResourceIds(userBridgeService.findResourcesIdsList(user.getId()));
String salt = user.getSalt();
String password = user.getPassWord();
return new SimpleAuthenticationInfo(shiroUser, password, ByteSource.Util.bytes(salt), getName());
}
/**
* @Description 授权方法
* @param principals SimpleAuthenticationInfo对象第一个参数
* @return
*/
@Override
public AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principals) {
ShiroUser shiroUser = (ShiroUser) principals.getPrimaryPrincipal();
return userBridgeService.getAuthorizationInfo(shiroUser);
}
/**
* @Description 加密方式
*/
@Override
public void initCredentialsMatcher() {
HashedCredentialsMatcher matcher = new HashedCredentialsMatcher(SuperConstant.HASH_ALGORITHM);
matcher.setHashIterations(SuperConstant.HASH_INTERATIONS);
setCredentialsMatcher(matcher);
}
}
【3.3】SimpleToken
package com.itheima.shiro.core.base;
import org.apache.shiro.authc.UsernamePasswordToken;
/**
* @Description 自定义tooken
*/
public class SimpleToken extends UsernamePasswordToken {
/** serialVersionUID */
private static final long serialVersionUID = -4849823851197352099L;
private String tokenType;
private String quickPassword;
/**
* Constructor for SimpleToken
* @param tokenType
*/
public SimpleToken(String tokenType, String username,String password) {
super(username,password);
this.tokenType = tokenType;
}
public SimpleToken(String tokenType, String username,String password,String quickPassword) {
super(username,password);
this.tokenType = tokenType;
this.quickPassword = quickPassword;
}
public String getTokenType() {
return tokenType;
}
public void setTokenType(String tokenType) {
this.tokenType = tokenType;
}
public String getQuickPassword() {
return quickPassword;
}
public void setQuickPassword(String quickPassword) {
this.quickPassword = quickPassword;
}
}
【3.4】ShiroUser
package com.itheima.shiro.core.base;
import com.itheima.shiro.utils.ToString;
import lombok.Data;
import java.util.List;
/**
* @Description 自定义Authentication对象,使得Subject除了携带用户的登录名外还可以携带更多信息
*/
@Data
public class ShiroUser extends ToString {
/** serialVersionUID */
private static final long serialVersionUID = -5024855628064590607L;
/**
* 主键
*/
private String id;
/**
* 登录名称
*/
private String loginName;
/**
* 真实姓名
*/
private String realName;
/**
* 昵称
*/
private String nickName;
/**
* 密码
*/
private String passWord;
/**
* 加密因子
*/
private String salt;
/**
* 性别
*/
private Integer sex;
/**
* 邮箱
*/
private String zipcode;
/**
* 地址
*/
private String address;
/**
* 固定电话
*/
private String tel;
/**
* 电话
*/
private String mobil;
/**
* 邮箱
*/
private String email;
/**
* 职务
*/
private String duties;
/**
* 排序
*/
private Integer sortNo;
/**
* 是否有效
*/
private String enableFlag;
private List<String> resourceIds;
public ShiroUser() {
super();
}
public ShiroUser(String id, String loginName) {
super();
this.id = id;
this.loginName = loginName;
}
@Override
public int hashCode() {
final int prime = 31;
int result = 1;
result = prime * result + ((email == null) ? 0 : email.hashCode());
result = prime * result + ((id == null) ? 0 : id.hashCode());
result = prime * result
+ ((loginName == null) ? 0 : loginName.hashCode());
result = prime * result + ((mobil == null) ? 0 : mobil.hashCode());
return result;
}
@Override
public boolean equals(Object obj) {
if (this == obj)
return true;
if (obj == null)
return false;
if (getClass() != obj.getClass())
return false;
ShiroUser other = (ShiroUser) obj;
if (email == null) {
if (other.email != null)
return false;
} else if (!email.equals(other.email))
return false;
if (id == null) {
if (other.id != null)
return false;
} else if (!id.equals(other.id))
return false;
if (loginName == null) {
if (other.loginName != null)
return false;
} else if (!loginName.equals(other.loginName))
return false;
if (mobil == null) {
if (other.mobil != null)
return false;
} else if (!mobil.equals(other.mobil))
return false;
return true;
}
}
【3.5】UserBridgeService
package com.itheima.shiro.core.bridge;
import com.itheima.shiro.core.base.ShiroUser;
import com.itheima.shiro.pojo.User;
import org.apache.shiro.authz.AuthorizationInfo;
import java.util.List;
/**
* @Description:用户信息桥接(后期会做缓存)
*/
public interface UserBridgeService {
/**
* @Description 查找用户信息
* @param loginName 用户名称
* @return user对象
*/
User findUserByLoginName(String loginName);
/**
* @Description 鉴权方法
* @param shiroUser 令牌对象
* @return 鉴权信息
*/
AuthorizationInfo getAuthorizationInfo(ShiroUser shiroUser);
/**
* @Description 查询用户对应角色标识list
* @param userId 用户id
* @return 角色标识集合
*/
List<String> findRoleList(String userId);
/**
* @Description 查询用户对应资源标识list
* @param userId 用户id
* @return 资源标识集合
*/
List<String> findResourcesList(String userId);
/**
* @Description 查询资源ids
* @param userId 用户id
* @return 资源id集合
*/
List<String> findResourcesIds(String userId);
}
【3.6】UserBridgeServiceImpl
package com.itheima.shiro.core.bridge.impl;
import com.itheima.shiro.core.adapter.UserAdapter;
import com.itheima.shiro.core.base.ShiroUser;
import com.itheima.shiro.core.bridge.UserBridgeService;
import com.itheima.shiro.pojo.Resource;
import com.itheima.shiro.pojo.Role;
import com.itheima.shiro.pojo.User;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Component;
import java.util.ArrayList;
import java.util.List;
/**
* @Description:用户信息桥接(后期会做缓存)
*/
@Component("userBridgeService")
public class UserBridgeServiceImpl implements UserBridgeService {
@Autowired
UserAdapter userAdapter;
@Override
public User findUserByLoginName(String loginName) {
return userAdapter.findUserByLoginName(loginName);
}
@Override
public AuthorizationInfo getAuthorizationInfo(ShiroUser shiroUser) {
//查询用户对应的角色标识
List<String> roleList = this.findRoleList(shiroUser.getId());
//查询用户对于的资源标识
List<String> resourcesList = this.findResourcesList(shiroUser.getId());
//构建鉴权信息对象
SimpleAuthorizationInfo simpleAuthorizationInfo = new SimpleAuthorizationInfo();
simpleAuthorizationInfo.addRoles(roleList);
simpleAuthorizationInfo.addStringPermissions(resourcesList);
return simpleAuthorizationInfo;
}
@Override
public List<String> findRoleList(String userId){
List<Role> roles = userAdapter.findRoleByUserId(userId);
List<String> roleLabel = new ArrayList<>();
for (Role role : roles) {
roleLabel.add(role.getLabel());
}
return roleLabel;
}
@Override
public List<String> findResourcesList(String userId){
List<Resource> resources = userAdapter.findResourceByUserId(userId);
List<String> resourceLabel = new ArrayList<>();
for (Resource resource : resources) {
resourceLabel.add(resource.getLabel());
}
return resourceLabel;
}
@Override
public List<String> findResourcesIds(String userId) {
List<Resource> resources = userAdapter.findResourceByUserId(userId);
List<String> ids = new ArrayList<>();
for (Resource resource : resources) {
ids.add(resource.getId());
}
return ids;
}
}
【3.7】UserAdapter
package com.itheima.shiro.core.adapter;
import com.itheima.shiro.pojo.Resource;
import com.itheima.shiro.pojo.Role;
import com.itheima.shiro.pojo.User;
import java.util.List;
/**
* @Description 后台登陆用户适配器接口
*/
public interface UserAdapter {
/**
* @Description 按用户名查找用户
* @param loginName 登录名
* @return
*/
User findUserByLoginName(String loginName);
/**
* @Description 查找用户所有角色
* @param userId 用户Id
* @return
*/
List<Role> findRoleByUserId(String userId);
/**
* @Description 查询用户有那些资源
* @param userId 用户Id
* @return
*/
List<Resource> findResourceByUserId(String userId);
}
【3.8】UserAdapterImpl
package com.itheima.shiro.core.adapter.impl;
import com.itheima.shiro.constant.SuperConstant;
import com.itheima.shiro.core.adapter.UserAdapter;
import com.itheima.shiro.mapper.UserMapper;
import com.itheima.shiro.mappercustom.UserAdapterMapper;
import com.itheima.shiro.pojo.Resource;
import com.itheima.shiro.pojo.Role;
import com.itheima.shiro.pojo.User;
import com.itheima.shiro.pojo.UserExample;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Component;
import java.util.HashMap;
import java.util.List;
import java.util.Map;
import java.util.concurrent.TimeUnit;
/**
* @Description 后台登陆用户适配器接口实现
*/
@Component("userAdapter")
public class UserAdapterImpl implements UserAdapter {
@Autowired
private UserMapper userMapper;
@Autowired
private UserAdapterMapper userAdapterMapper;
@Override
public User findUserByLoginName(String loginName) {
UserExample userExample = new UserExample();
userExample.createCriteria().andEnableFlagEqualTo(SuperConstant.YES).andLoginNameEqualTo(loginName);
List<User> userList = userMapper.selectByExample(userExample);
if (userList.size()==1) {
return userList.get(0);
}else {
return null;
}
}
@Override
public List<Role> findRoleByUserId(String userId) {
Map<String, Object> values = new HashMap<String, Object>();
values.put("userId", userId);
values.put("enableFlag", SuperConstant.YES);
List<Role> list = userAdapterMapper.findRoleByUserId(values);
return list;
}
@Override
public List<Resource> findResourceByUserId(String userId) {
Map<String, Object> values = new HashMap<String, Object>();
values.put("userId", userId);
values.put("enableFlag", SuperConstant.YES);
List<Resource> list=userAdapterMapper.findResourceByUserId(values);
return list;
}
}
5、ShiroConfig配置
【1】图解
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-3g0DS3BG-1665144667177)(image/1581064915787.png)]
【2】原理分析
(1)、创建SimpleCookie,访问项目时,会在客户端中cookie中存放ShiroSession的对
(2)、创建DefaultWebSessionManager会话管理器定义cookie机制、定时刷新、全局会话超时时间然后交
于DefaultWebSecurityManager权限管理器管理
(3)、创建自定义ShiroDbRealm实现,用于权限认证、授权、加密方式的管理,同时从数据库中取得相关的
角色、资源、用户的信息,然后交于DefaultWebSecurityManager权限管理器管理
(4)、创建DefaultWebSecurityManager权限管理器用于管理DefaultWebSessionManager会话管理器、ShiroDbRealm
(5)、创建lifecycleBeanPostProcessor和DefaultAdvisorAutoProxyCreator相互配合事项注解的权限鉴权
(6)、创建ShiroFilterFactoryBean的shiro过滤器指定权限管理器、同时启动连接链及登录URL、未登录的URL
的跳转
【3】ShiroConfig代码
package com.itheima.shiro.config;
import com.itheima.shiro.core.ShiroDbRealm;
import com.itheima.shiro.core.impl.ShiroDbRealmImpl;
import com.itheima.shiro.properties.PropertiesUtil;
import lombok.extern.log4j.Log4j2;
import org.apache.shiro.spring.LifecycleBeanPostProcessor;
import org.apache.shiro.spring.security.interceptor.AuthorizationAttributeSourceAdvisor;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.apache.shiro.web.servlet.SimpleCookie;
import org.apache.shiro.web.session.mgt.DefaultWebSessionManager;
import org.springframework.aop.framework.autoproxy.DefaultAdvisorAutoProxyCreator;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.ComponentScan;
import org.springframework.context.annotation.Configuration;
import org.springframework.context.annotation.DependsOn;
import java.util.LinkedHashMap;
import java.util.List;
import java.util.Map;
/**
* @Description:权限配置类
*/
@Configuration
@ComponentScan(basePackages = "com.itheima.shiro.core")
@Log4j2
public class ShiroConfig {
/**
* @Description 创建cookie对象
*/
@Bean(name="sessionIdCookie")
public SimpleCookie simpleCookie(){
SimpleCookie simpleCookie = new SimpleCookie();
simpleCookie.setName("ShiroSession");
return simpleCookie;
}
/**
* @Description 权限管理器
*/
@Bean(name="securityManager")
public DefaultWebSecurityManager defaultWebSecurityManager(){
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
securityManager.setRealm(shiroDbRealm());
securityManager.setSessionManager(shiroSessionManager());
return securityManager;
}
/**
* @Description 自定义RealmImpl
*/
@Bean(name="shiroDbRealm")
public ShiroDbRealm shiroDbRealm(){
return new ShiroDbRealmImpl();
}
/**
* @Description 会话管理器
*/
@Bean(name="sessionManager")
public DefaultWebSessionManager shiroSessionManager(){
DefaultWebSessionManager sessionManager = new DefaultWebSessionManager();
sessionManager.setSessionValidationSchedulerEnabled(false);
sessionManager.setSessionIdCookieEnabled(true);
sessionManager.setSessionIdCookie(simpleCookie());
sessionManager.setGlobalSessionTimeout(3600000);
return sessionManager;
}
/**
* @Description 保证实现了Shiro内部lifecycle函数的bean执行
*/
@Bean(name = "lifecycleBeanPostProcessor")
public static LifecycleBeanPostProcessor getLifecycleBeanPostProcessor() {
return new LifecycleBeanPostProcessor();
}
/**
* @Description AOP式方法级权限检查
*/
@Bean
@DependsOn("lifecycleBeanPostProcessor")
public DefaultAdvisorAutoProxyCreator getDefaultAdvisorAutoProxyCreator() {
DefaultAdvisorAutoProxyCreator defaultAdvisorAutoProxyCreator = new DefaultAdvisorAutoProxyCreator();
defaultAdvisorAutoProxyCreator.setProxyTargetClass(true);
return defaultAdvisorAutoProxyCreator;
}
/**
* @Description 配合DefaultAdvisorAutoProxyCreator事项注解权限校验
*/
@Bean
public AuthorizationAttributeSourceAdvisor getAuthorizationAttributeSourceAdvisor() {
AuthorizationAttributeSourceAdvisor aasa = new AuthorizationAttributeSourceAdvisor();
aasa.setSecurityManager(defaultWebSecurityManager());
return new AuthorizationAttributeSourceAdvisor();
}
/**
* @Description 过滤器链
*/
private Map<String, String> filterChainDefinition(){
List<Object> list = PropertiesUtil.propertiesShiro.getKeyList();
Map<String, String> map = new LinkedHashMap<>();
for (Object object : list) {
String key = object.toString();
String value = PropertiesUtil.getShiroValue(key);
log.info("读取防止盗链控制:---key{},---value:{}",key,value);
map.put(key, value);
}
return map;
}
/**
* @Description Shiro过滤器
*/
@Bean("shiroFilter")
public ShiroFilterFactoryBean shiroFilterFactoryBean(){
ShiroFilterFactoryBean shiroFilter = new ShiroFilterFactoryBean();
shiroFilter.setSecurityManager(defaultWebSecurityManager());
shiroFilter.setFilterChainDefinitionMap(filterChainDefinition());
shiroFilter.setLoginUrl("/login");
shiroFilter.setUnauthorizedUrl("/login");
return shiroFilter;
}
}
6、Shiro过滤器、过滤器链
【1】过滤器
Shiro内置了很多默认的过滤器,比如身份验证、授权等相关的。默认过滤器可以参考org.apache.shiro.web.filter.mgt.DefaultFilter中的枚举过滤器

【2】过滤器链
定义:authentication.properties
#静态资源不过滤
/static/**=anon
#登录链接不过滤
/login/**=anon
#其他链接是需要登录的
/**=authc
注意:这里定义的过滤器是有执行顺序的,从上向下执行
【3】加载原理分析
定义:PropertiesUtil,从classpath中加载authentication.properties
package com.itheima.shiro.properties;
import com.itheima.shiro.utils.EmptyUtil;
import lombok.extern.log4j.Log4j2;
/**
* @Description 读取Properties的工具类
*/
@Log4j2
public class PropertiesUtil {
public static LinkProperties propertiesShiro = new LinkProperties();
/**
* 读取properties配置文件信息
*/
static {
String sysName = System.getProperty("sys.name");
if (EmptyUtil.isNullOrEmpty(sysName)) {
sysName = "application.properties";
} else {
sysName += ".properties";
}
try {
propertiesShiro.load(PropertiesUtil.class.getClassLoader()
.getResourceAsStream("authentication.properties"));
} catch (Exception e) {
log.warn("资源路径中不存在authentication.properties权限文件,忽略读取!");
}
}
/**
* 根据key得到value的值
*/
public static String getShiroValue(String key) {
return propertiesShiro.getProperty(key);
}
}
定义LinkProperties,这个类保证了Properties类的有序
package com.itheima.shiro.properties;
import java.io.*;
import java.util.ArrayList;
import java.util.Enumeration;
import java.util.List;
import java.util.Properties;
/**
* @Description 有序Properties类
*/
public class LinkProperties extends Properties{
/** serialVersionUID */
private static final long serialVersionUID = 7573016303908223266L;
private List<Object> keyList = new ArrayList<Object>();
/**
* 默认构造方法
*/
public LinkProperties() {
}
/**
* 从指定路径加载信息到Properties
* @param path
*/
public LinkProperties(String path) {
try {
InputStream is = new FileInputStream(path);
this.load(is);
} catch (FileNotFoundException e) {
e.printStackTrace();
throw new RuntimeException("指定文件不存在!");
} catch (IOException e) {
e.printStackTrace();
}
}
/**
* 重写put方法,按照property的存入顺序保存key到keyList,遇到重复的后者将覆盖前者。
*/
@Override
public synchronized Object put(Object key, Object value) {
this.removeKeyIfExists(key);
keyList.add(key);
return super.put(key, value);
}
/**
* 重写remove方法,删除属性时清除keyList中对应的key。
*/
@Override
public synchronized Object remove(Object key) {
this.removeKeyIfExists(key);
return super.remove(key);
}
/**
* keyList中存在指定的key时则将其删除
*/
private void removeKeyIfExists(Object key) {
keyList.remove(key);
}
/**
* 获取Properties中key的有序集合
* @return
*/
public List<Object> getKeyList() {
return keyList;
}
/**
* 保存Properties到指定文件,默认使用UTF-8编码
* @param path 指定文件路径
*/
public void store(String path) {
this.store(path, "UTF-8");
}
/**
* 保存Properties到指定文件,并指定对应存放编码
* @param path 指定路径
* @param charset 文件编码
*/
public void store(String path, String charset) {
if (path != null && !"".equals(path)) {
try {
OutputStream os = new FileOutputStream(path);
BufferedWriter bw = new BufferedWriter(new OutputStreamWriter(os, charset));
this.store(bw, null);
bw.close();
} catch (FileNotFoundException e) {
e.printStackTrace();
} catch (IOException e) {
e.printStackTrace();
}
} else {
throw new RuntimeException("存储路径不能为空!");
}
}
/**
* 重写keys方法,返回根据keyList适配的Enumeration,且保持HashTable keys()方法的原有语义,
* 每次都调用返回一个新的Enumeration对象,且和之前的不产生冲突
*/
@Override
public synchronized Enumeration<Object> keys() {
return new EnumerationAdapter<Object>(keyList);
}
/**
* List到Enumeration的适配器
*/
private class EnumerationAdapter<T> implements Enumeration<T> {
private int index = 0;
private final List<T> list;
private final boolean isEmpty;
public EnumerationAdapter(List<T> list) {
this.list = list;
this.isEmpty = list.isEmpty();
}
public boolean hasMoreElements() {
//isEmpty的引入是为了更贴近HashTable原有的语义,在HashTable中添加元素前调用其keys()方法获得一个Enumeration的引用,
//之后往HashTable中添加数据后,调用之前获取到的Enumeration的hasMoreElements()将返回false,但如果此时重新获取一个
//Enumeration的引用,则新Enumeration的hasMoreElements()将返回true,而且之后对HashTable数据的增、删、改都是可以在
//nextElement中获取到的。
return !isEmpty && index < list.size();
}
public T nextElement() {
if (this.hasMoreElements()) {
return list.get(index++);
}
return null;
}
}
}
查看shirocConfig

加载完整之后交于ShiroFilterFactoryBean使用setFilterChainDefinitionMap使得过滤生效
【4】自定义过滤器
上面我们使用了shiro的默认过滤器,但是由于业务需求,咱们可能要定义自己的过滤器,那么咱们定义呢?
这里我们先查看RolesAuthorizationFilter
分析:改源码表示,例如:/admin/order= roles[“admin, root”] ,只有当放问该接口同时具备admin和root两种角色时,才可以被访问。
【5】自定义过滤器使用
【5.1】需求
1、实现只要有其中一个角色,则可访问对应路径
【5.2】RolesOrAuthorizationFilter
新建filter层,新建类RolesOrAuthorizationFilter
package com.itheima.shiro.filter;
import org.apache.shiro.subject.Subject;
import org.apache.shiro.util.CollectionUtils;
import org.apache.shiro.web.filter.authz.AuthorizationFilter;
import javax.servlet.ServletRequest;
import javax.servlet.ServletResponse;
import java.io.IOException;
import java.util.Set;
/**
* @Description:角色或关系
*/
public class RolesOrAuthorizationFilter extends AuthorizationFilter {
//TODO - complete JavaDoc
@SuppressWarnings({"unchecked"})
public boolean isAccessAllowed(ServletRequest request, ServletResponse response, Object mappedValue) throws IOException {
Subject subject = getSubject(request, response);
String[] rolesArray = (String[]) mappedValue;
if (rolesArray == null || rolesArray.length == 0) {
//no roles specified, so nothing to check - allow access.
return true;
}
Set<String> roles = CollectionUtils.asSet(rolesArray);
//循环roles判断只要有角色则返回true
for (String role : roles) {
if(subject.hasRole(role)){
return true;
}
}
return false;
}
}
【5.3】编辑ShiroConfig
在ShiroConfig类中添加如下内容
/**
* @Description 自定义过滤器定义
*/
private Map<String, Filter> filters() {
Map<String, Filter> map = new HashMap<String, Filter>();
map.put("role-or", new RolesOrAuthorizationFilter());
return map;
}
/**
* @Description Shiro过滤器
*/
@Bean("shiroFilter")
public ShiroFilterFactoryBean shiroFilterFactoryBean(){
ShiroFilterFactoryBean shiroFilter = new ShiroFilterFactoryBean();
shiroFilter.setSecurityManager(defaultWebSecurityManager());
//使自定义过滤器生效
shiroFilter.setFilters(filters());
shiroFilter.setFilterChainDefinitionMap(filterChainDefinition());
shiroFilter.setLoginUrl("/login");
shiroFilter.setUnauthorizedUrl("/login");
return shiroFilter;
}
【2.2.3】编辑authentication.properties
#静态资源不过滤
/static/**=anon
#登录链接不过滤
/login/**=anon
#访问/resource/**需要有admin的角色
/resource/**=role-or[admin]
#其他链接是需要登录的
/**=authc
7、注解方式鉴权
【1】注解介绍
以下为常用注解
| 注解 | 说明 |
|---|---|
| @RequiresAuthentication | 表明当前用户需是经过认证的用户 |
| @ RequiresGuest | 表明该用户需为”guest”用户 |
| @RequiresPermissions | 当前用户需拥有指定权限 |
| @RequiresRoles | 当前用户需拥有指定角色 |
| @ RequiresUser | 当前用户需为已认证用户或已记住用户 |
例如RoleAction类中我们添加
/**
*@Description: 跳转到角色的初始化页面
*/
@RequiresRoles(value ={"SuperAdmin","dev"},logical = Logical.OR)
@RequestMapping(value = "listInitialize")
public ModelAndView listInitialize(){
return new ModelAndView("/role/role-listInitialize");
}
【2】注解原理分析
【2.1】装载过程
【2.2】调用过程
更多推荐
 已为社区贡献8条内容
已为社区贡献8条内容






所有评论(0)